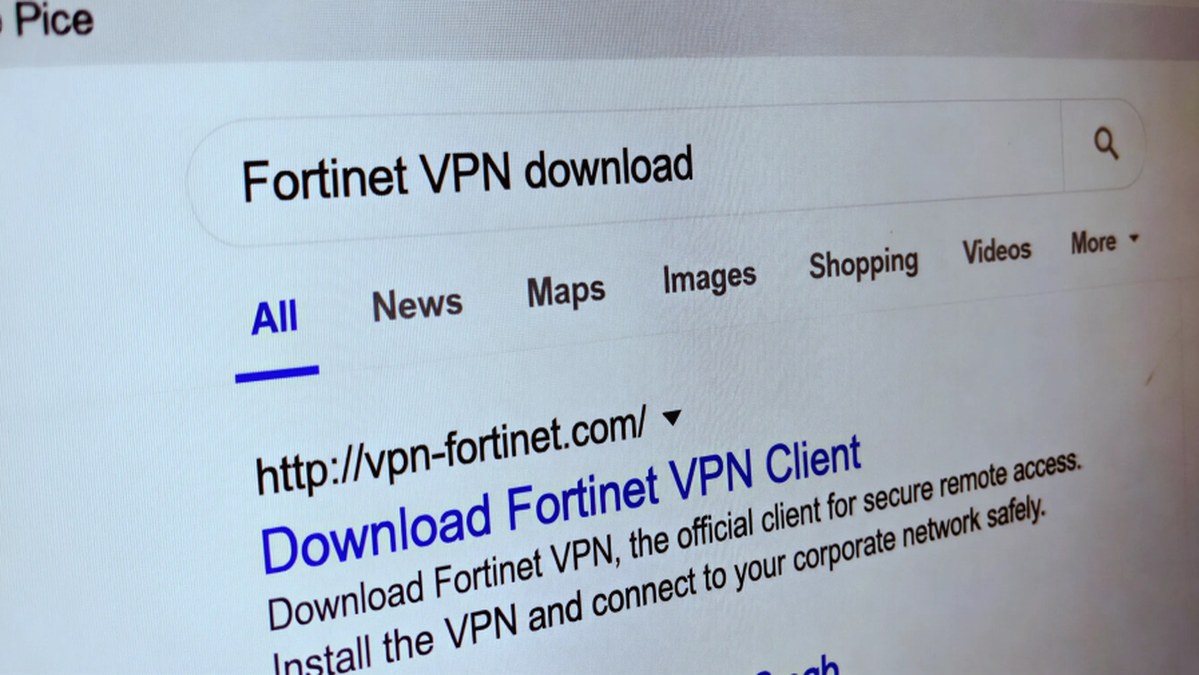
Microsoft has detailed a sophisticated credential theft campaign attributed to the threat actor cluster Storm-2561. The operation leverages search engine optimization (SEO) poisoning techniques to distribute fake virtual private network (VPN) clients. According to Microsoft's Threat Intelligence and Defender Experts teams, the campaign redirects users searching for legitimate enterprise software to malicious ZIP files hosted on attacker-controlled websites. These files deploy digitally signed trojans that impersonate trusted VPN clients while simultaneously harvesting sensitive VPN credentials from the victim's system. Microsoft first observed this activity in mid-January 2026.
Storm-2561, active since at least May 2025, has a documented history of using SEO poisoning to impersonate popular software vendors. Earlier campaigns, first documented by cybersecurity firm Cyjax, involved redirecting users searching for software from companies like SonicWall, Hanwha Vision, and Pulse Secure (now Ivanti Secure Access) on the Bing search engine. Users were led to fake websites and tricked into downloading MSI installers that deployed the Bumblebee malware loader. A subsequent iteration of the attack, disclosed by Zscaler in October 2025, specifically targeted users searching for Ivanti Pulse Secure VPN software, propagating a trojanized client through a deceptive domain ("ivanti-vpn[.]org") designed to steal credentials.
This campaign underscores a critical social engineering tactic: exploiting user trust in search engine rankings and established software brands. Threat actors manipulate search results to place their malicious sites prominently, capitalizing on the assumption that top results are legitimate. The attack chain is further enabled by the abuse of trusted platforms, notably GitHub, which is used to host the malicious installer files. The repository contains a ZIP file with an MSI installer that appears to be legitimate VPN software but, during installation, sideloads malicious DLL files to facilitate credential theft.
The technical execution involves a multi-stage process. The malicious MSI installer, often digitally signed to appear trustworthy, is the initial payload. Once executed, it sideloads a malicious DLL file. This DLL is responsible for the core malicious functionality: harvesting stored VPN credentials from the victim's machine. The collected data is then exfiltrated to attacker-controlled servers. The end goal remains consistent across Storm-2561's operations: to steal enterprise VPN credentials, which can provide a foothold into corporate networks for further intrusion, data theft, or ransomware deployment.
Organizations and individuals searching for enterprise software must exercise heightened caution. Security recommendations include verifying software download URLs directly with the official vendor's website, being wary of search results that lead to unfamiliar domains, and scrutinizing digital signatures (though these can also be stolen or forged). Network defenders should monitor for suspicious outbound connections from endpoints and implement application allowlisting to prevent the execution of unauthorized installers. This campaign is a stark reminder that even trusted platforms and search engines can be weaponized in the attack chain, necessitating a defense-in-depth approach to cybersecurity.