EXCLUSIVE: RUST REVOLUTION IN CYBERCRIME AS AI-POWERED MALWARE VENON HITS 33 BANKS
A new, highly sophisticated banking malware written in Rust is tearing through Brazil's financial sector, signaling a dangerous evolution in Latin American cybercrime. Dubbed VENON, this threat marks a stark departure from the region's traditional Delphi-based malware families, introducing a level of technical prowess that has cybersecurity experts deeply alarmed. Its primary weapon is credential-stealing overlays, deployed against customers of 33 major Brazilian banks.
VENON's infection chain is a masterclass in deception and evasion. It begins with a sophisticated phishing campaign, likely using social engineering lures like fake software updates, to deliver a malicious ZIP archive. Once executed via a PowerShell script, the malware employs DLL side-loading to launch its payload. Before any theft begins, VENON executes nine advanced evasion techniques, including anti-sandbox checks and AMSI bypass, to slip past modern defenses undetected.
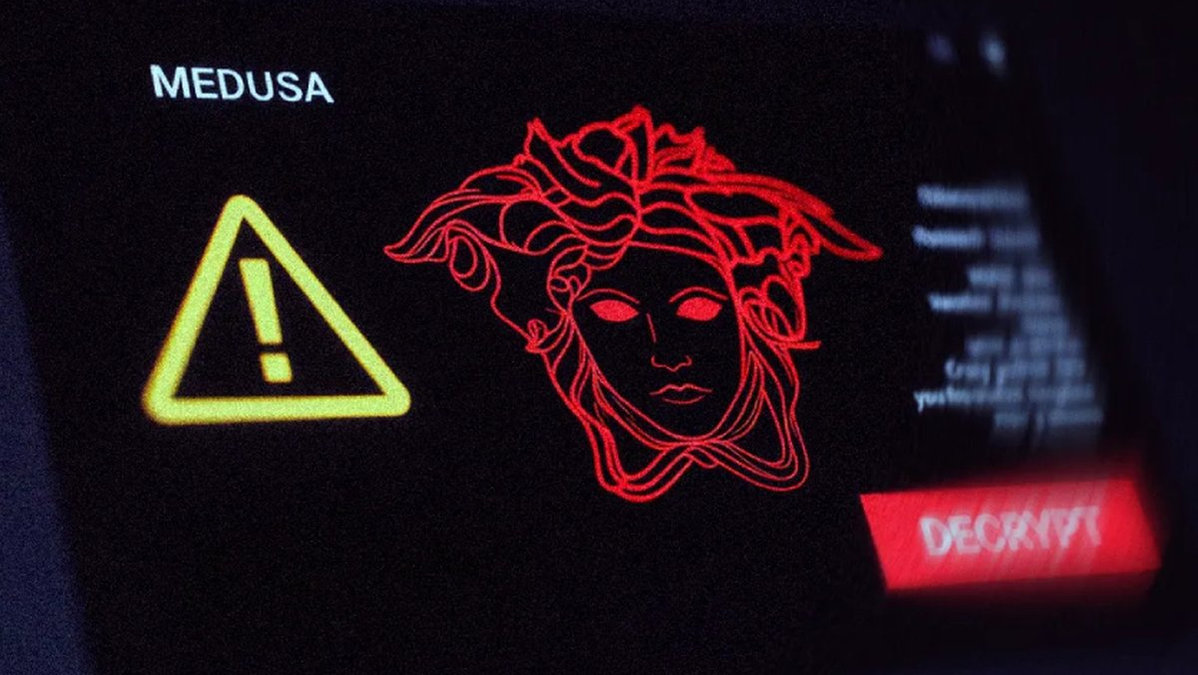
What truly sets this operation apart is its suspected genesis. Researchers analyzing the Rust code structure see patterns suggesting a developer used generative AI to rewrite and expand the capabilities of established trojans like Grandoreiro into this new, more powerful form. "This isn't just a new malware; it's a new methodology. We're seeing the weaponization of AI to create more resilient and sophisticated exploits, potentially lowering the barrier for serious cybercrime," revealed a senior threat intelligence analyst familiar with the investigation.
For the global cybersecurity community, VENON is a five-alarm fire. It demonstrates that threat actors are rapidly adopting secure programming languages like Rust to build stealthier malware, while potentially leveraging AI to accelerate development. This creates a potent recipe for more frequent and damaging data breaches. The malware's advanced tactics, including indirect syscalls and ETW bypass, will soon become standard, challenging existing detection paradigms.
The discovery of developer environment paths pointing to a username "byst4" offers a rare forensic clue, but the group itself remains unattributed and at large. With its capability to hijack banking app shortcuts and establish a persistent WebSocket connection to its command server, VENON represents a clear and present danger. Its very design, including an uninstall function to remove traces, shows professional-grade planning.
The crypto and blockchain security sectors should take note: the techniques being perfected here for stealing fiat currency credentials will inevitably be turned toward digital asset wallets. This Rust-based threat is the future of financial cybercrime, and that future is now. The age of AI-assisted, professionally coded malware has officially begun.