EXCLUSIVE: NORTH KOREA'S CYBER ARMY UNLEASHES CRYPTO-FUNDED WMD PROGRAM, EXPOSING CRITICAL BLOCKCHAIN SECURITY VULNERABILITIES
A silent, digital war is funding weapons of mass destruction. The U.S. Treasury has exposed a sprawling network of North Korean IT workers infiltrating global tech firms, funneling millions in stolen cryptocurrency directly to Pyongyang's banned WMD programs. This isn't just sanctions evasion; it's a state-sponsored heist enabled by systemic weaknesses in our digital financial infrastructure.
These operatives use sophisticated social engineering and phishing campaigns to gain employment, then deploy malware and exploit zero-day vulnerabilities to siphon funds. The proceeds are laundered through complex crypto transactions, exploiting gaps in compliance to finance a nuclear arsenal. This represents a catastrophic convergence of cybersecurity failure and national security threat.
"North Korea has weaponized the crypto ecosystem," reveals a senior intelligence analyst working on trace investigations. "They are not just stealing coins; they are actively probing for and exploiting critical vulnerabilities in blockchain security protocols to obfuscate the flow of funds. Every unreported ransomware payment, every unpatched system, indirectly funds a missile test."
Why should you care? This digital battlefield funds real-world terror. The malware that locks a hospital's systems and the phishing email targeting a crypto exchange are now directly linked to nuclear proliferation. The tools for tracing these funds exist, but adoption is fragmented, leaving dangerous blind spots.
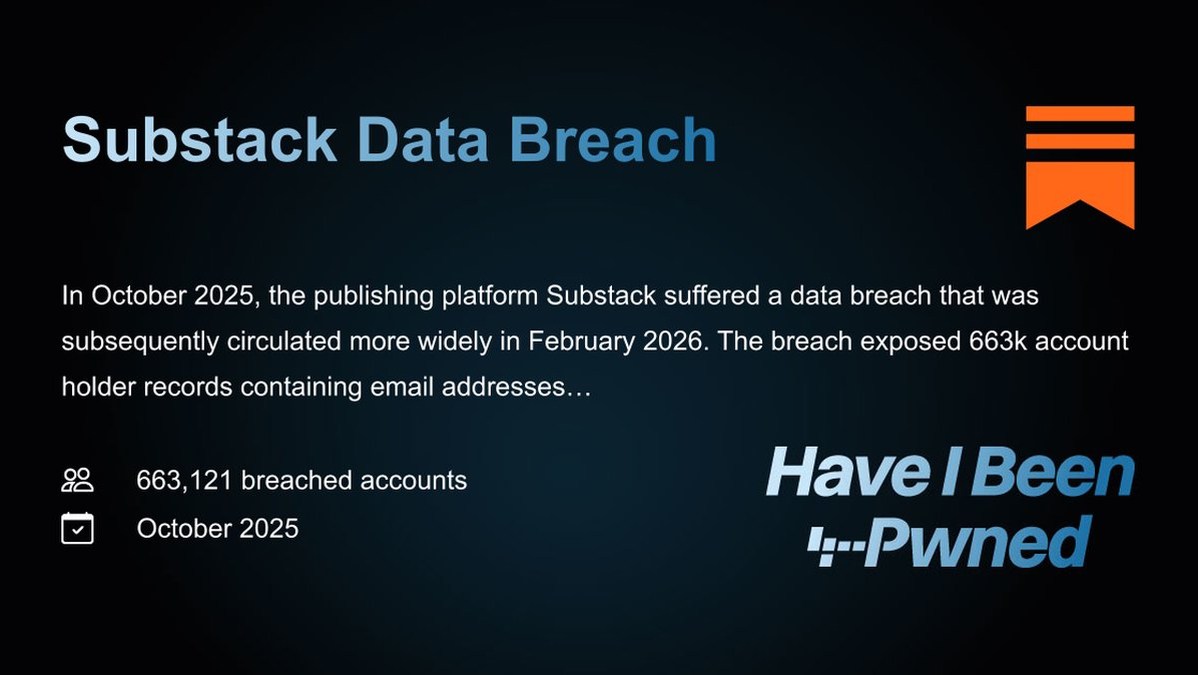
We predict a surge in regulatory action mandating real-time transaction monitoring for all virtual asset service providers. The era of optional compliance is over. The next major international data breach will be traced directly to a nation-state's weapons program.
Your digital wallet is now a matter of global security.