The cybersecurity landscape this week was defined by a stark duality: significant victories for defenders countered by the relentless innovation of threat actors. Law enforcement and security firms achieved notable successes in dismantling critical criminal infrastructure, while researchers disclosed severe vulnerabilities in foundational technologies and documented novel attack methodologies. This cycle of action and reaction underscores the perpetual arms race that defines modern digital security.
In a major coordinated action, a coalition led by Europol and involving companies like Proofpoint successfully dismantled the infrastructure supporting the Tycoon2FA phishing-as-a-service (PhaaS) platform. Tycoon2FA was identified as one of the world's largest adversary-in-the-middle (AitM) phishing operations, specializing in bypassing multi-factor authentication (MFA). These PhaaS platforms have become a critical enabler for cybercrime, commoditizing sophisticated attacks by providing less-skilled actors with kits to create convincing phishing pages and emails. In a parallel operation, authorities also took down LeakBase, a prominent online forum serving as a marketplace for stolen data and criminal collaboration. These takedowns represent a tangible blow to the cybercriminal ecosystem's logistical and economic support structures.
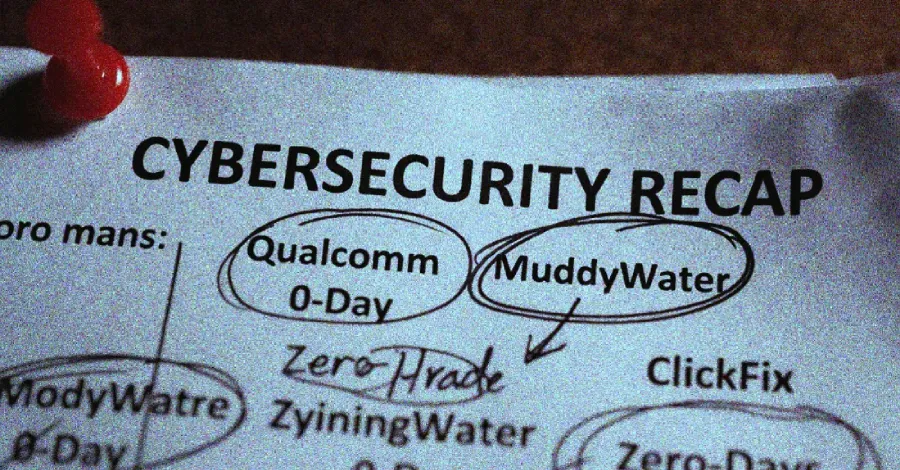
However, the threat horizon simultaneously expanded with the disclosure of critical vulnerabilities. Google's Threat Analysis Group (TAG) revealed an exploit chain targeting iOS, leveraging three zero-day vulnerabilities (CVE-2024-23296, CVE-2024-23274, and CVE-2024-23222) to achieve kernel code execution. This sophisticated chain, distributed via malicious iMessages, enabled complete device compromise. Separately, Qualcomm addressed a severe high-impact vulnerability (CVE-2023-33106) in its Adreno GPU driver, which could allow a local attacker to gain kernel privileges. These flaws in core hardware and software components highlight the pervasive attack surface that defenders must monitor.
Further demonstrating attacker ingenuity, researchers unveiled the "AirSnitch" attack, a novel side-channel technique that exploits Wi-Fi management frames to infer a user's active app usage on iOS and Android devices, posing a significant privacy risk. Meanwhile, a new malware campaign showcased "vibe-coding" tactics, where threat actors hide malicious PowerShell commands within the comments of software repositories, leveraging the trust associated with open-source platforms to evade detection. These developments illustrate a continuous evolution in both technical exploitation and social engineering tactics.
The week's events present a clear narrative: while proactive takedowns and patches are crucial defensive wins, the underlying trend points toward an increasing professionalization and specialization of threats. From PhaaS economies-of-scale to hardware-level vulnerabilities and novel side-channel attacks, the arsenal available to adversaries is both broadening and deepening. For security professionals, this underscores the non-negotiable need for layered defense-in-depth, rigorous patch management, and user education to mitigate risks across the entire threat spectrum.