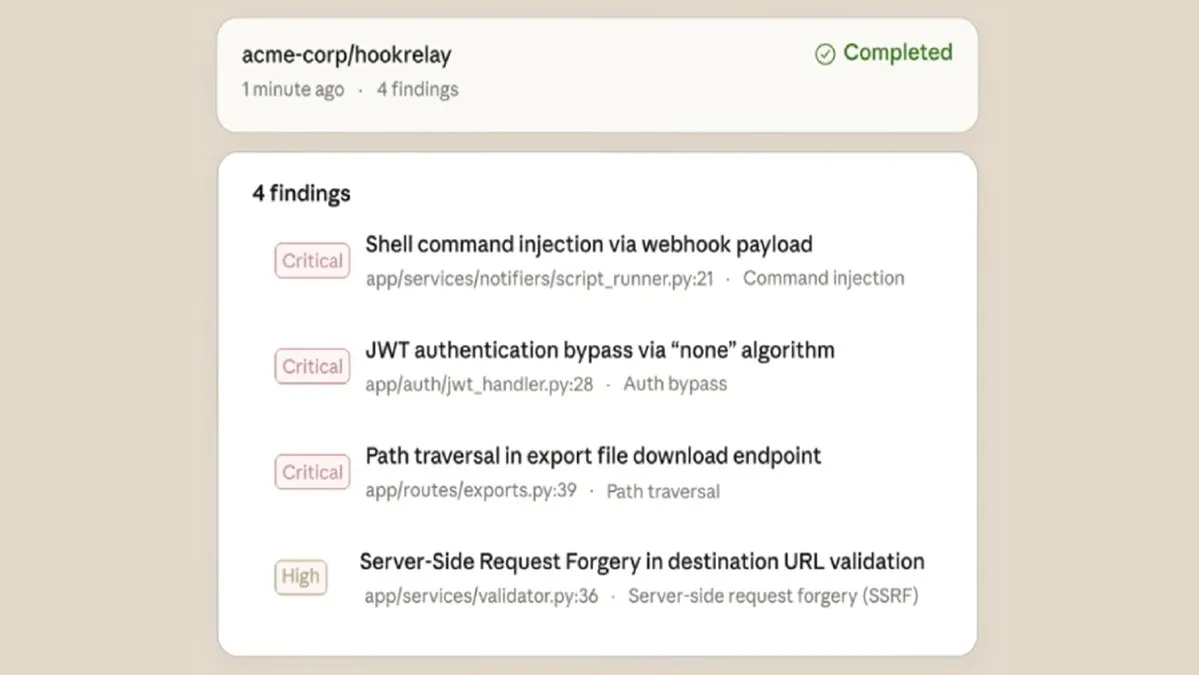
The intersection of cybersecurity incidents and traditional legal doctrines is becoming a critical battleground for organizations seeking recourse after an attack. A recent legal analysis highlights the significant challenge posed by the economic loss doctrine in negligence claims following a ransomware attack. This common law principle typically bars recovery for purely economic losses—such as lost profits, operational downtime, and remediation costs—in a negligence suit unless accompanied by physical property damage or bodily injury. In the context of a ransomware attack, which primarily encrypts data and disrupts digital operations, plaintiffs often struggle to demonstrate the tangible, physical harm required to circumvent this doctrinal bar. This creates a substantial legal hurdle for businesses aiming to hold third-party vendors, software providers, or managed service providers accountable for security failures that led to a breach.
The application of the economic loss doctrine forces a reevaluation of how "property" is defined in the digital age. Courts have historically been reluctant to classify corrupted data or locked systems as physical property damage, viewing them instead as intangible economic interests. Consequently, a business that suffers massive financial loss due to a ransomware infection may find its negligence claim dismissed if its only alleged damages are financial. This legal reality underscores the importance of contractual risk allocation. Organizations are increasingly advised to fortify their service agreements with explicit cybersecurity warranties, indemnification clauses, and detailed provisions outlining liability for security incidents. A well-drafted contract can provide a clearer path to compensation than reliance on tort-based negligence claims alone.
For legal professionals and cybersecurity teams, this evolving landscape necessitates a dual-focused strategy. Proactively, organizations must conduct rigorous due diligence on partners and insist on robust contractual safeguards that define security standards and breach responsibilities. Reactively, in the event of an attack, the response must include a immediate forensic investigation to determine the attack vector and potentially identify a negligent party, while also meticulously documenting all forms of loss. While some jurisdictions may recognize certain types of digital intrusion as constituting harm sufficient to overcome the economic loss rule, relying on this is risky. The most prudent course is to assume the doctrine will apply and to build legal and operational strategies—centered on strong contracts and comprehensive cyber insurance—that do not depend on successfully navigating this significant legal obstacle.