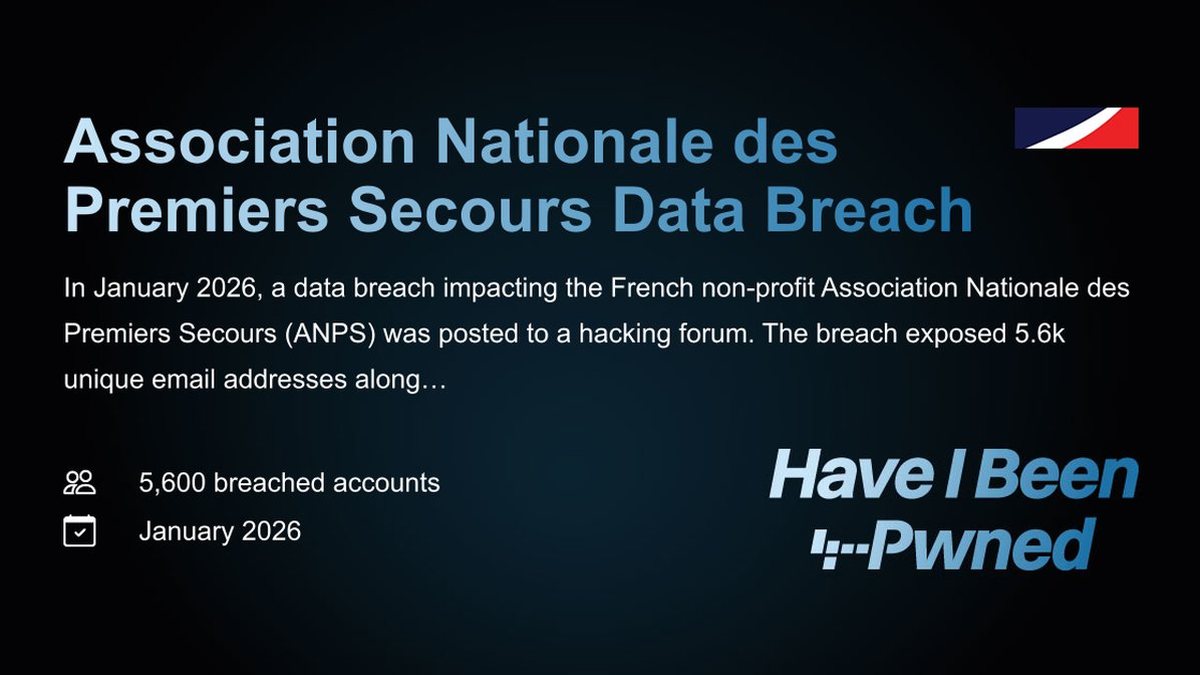
A sophisticated, years-long cyber espionage campaign has been targeting high-value organizations across South, Southeast, and East Asia. The victims span critical sectors including aviation, energy, government, law enforcement, pharmaceuticals, technology, and telecommunications. Security researchers from Palo Alto Networks Unit 42 have attributed this activity to a previously undocumented threat group, which they have designated CL-UNK-1068. The "CL" stands for cluster, and "UNK" indicates the group's core motivation remains formally unknown. However, Unit 42 assesses with moderate-to-high confidence that the primary objective of this persistent campaign is cyber espionage, aimed at stealing sensitive information for strategic advantage.
The adversary employs a multi-faceted and pragmatic toolset designed for stealth and persistence. According to Unit 42 security researcher Tom Fakterman, this arsenal includes custom-developed malware, strategically modified open-source utilities, and living-off-the-land binaries (LOLBINs). This approach allows the attackers to blend in with normal system activity, using legitimate tools already present on the network to perform malicious actions, thereby reducing their footprint and complicating detection. The tools are engineered to operate in both Windows and Linux environments, demonstrating the group's flexibility in targeting diverse IT infrastructures. Key components of their toolkit include known malware families like the Godzilla and ANTSWORD web shells, the Linux backdoor Xnote, and the Fast Reverse Proxy (FRP) tool for creating covert tunnels.
The attack methodology typically begins with the exploitation of vulnerabilities in public-facing web servers. Once initial access is gained, the attackers deploy web shells like Godzilla or ANTSWORD to establish a foothold. They then move laterally across the network to other hosts. A key focus of their post-compromise activity is the theft of specific files from Windows web servers, particularly from the `c:\inetpub\wwwroot` directory. They systematically search for and exfiltrate files with extensions such as `.web.config`, `.aspx`, `.asmx`, `.asax`, and `.dll`. This pattern suggests a concerted effort to harvest web application configuration files, source code, and binaries, likely to extract embedded credentials, discover hardcoded secrets, or identify software vulnerabilities for further exploitation.
Beyond web server files, the threat actor, CL-UNK-1068, casts a wide net for valuable data. Their collection efforts extend to stealing web browser history and bookmarks from compromised systems, which can reveal user behaviors, accessed internal resources, and credentials saved in browsers. Additionally, they target productivity documents, specifically seeking out XLSX and CSV files from user desktops and profile directories. These files often contain structured data, financial information, employee details, or operational plans—all high-value intelligence for espionage purposes. The use of tools like Xnote, a backdoor historically linked to the Chinese group Earth Berberoka (GamblingPuppet), alongside other utilities common in Chinese cyber operations, provides strong circumstantial evidence pointing to the actor's origin, aligning with a pattern of state-aligned cyber espionage targeting Asia's critical infrastructure.