The Federal Bureau of Investigation (FBI) has issued a stark warning regarding a targeted phishing campaign where cybercriminals are impersonating U.S. city and county planning and zoning officials. This scheme specifically targets businesses and individuals with active applications for land-use permits. According to a public service announcement, the attackers leverage publicly available information—such as permit details, application numbers, and property addresses—to craft highly convincing fraudulent emails. These emails fraudulently request payment for permit-related fees, directing victims to make payments via wire transfer, peer-to-peer payment apps, or cryptocurrency, thereby creating a significant financial fraud risk.
The sophistication of this campaign lies in its use of open-source intelligence (OSINT). By incorporating legitimate, publicly accessible details about a victim's permit application, the malicious emails bypass initial scrutiny and appear authentic. Common red flags identified by the FBI include emails originating from non-governmental domains (e.g., @usa.com instead of a legitimate .gov address), attachments that instruct recipients to email for further details—a tactic to establish direct communication—and high-pressure tactics urging immediate payment to avoid purported permit delays or cancellations. This social engineering approach preys on the urgency and bureaucratic nature of permit processes.
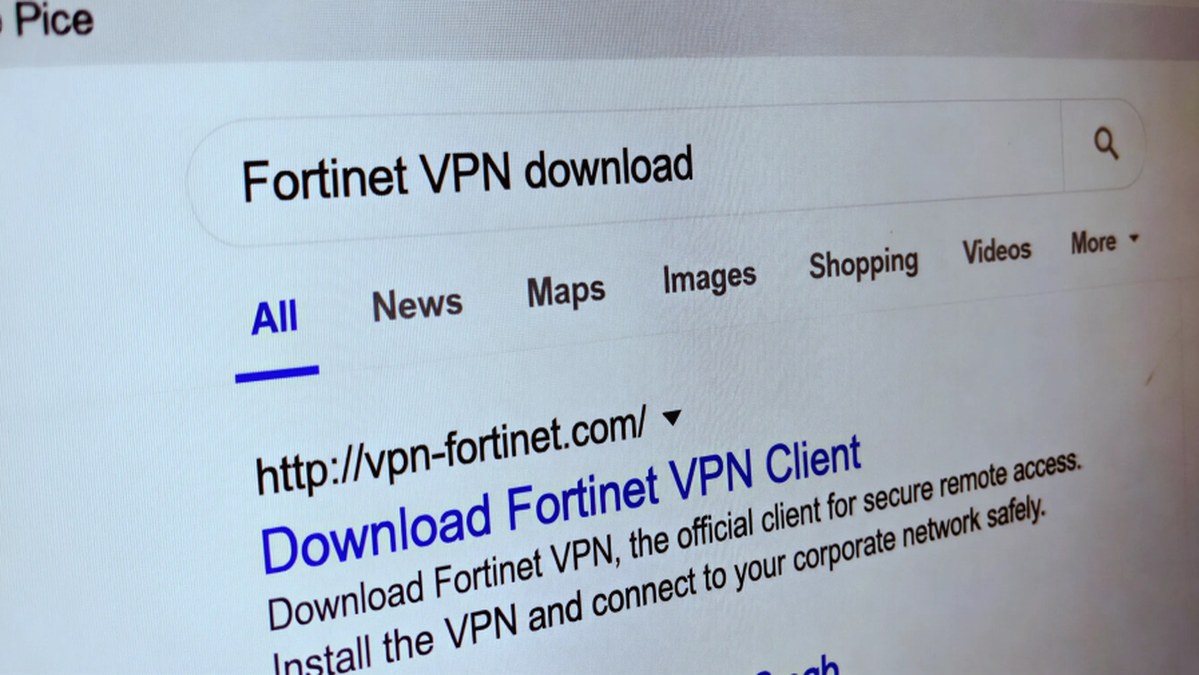
This warning arrives amidst a broader landscape of evolving cyber threats. As highlighted in other recent reports, adversaries are increasingly abusing infrastructure like .arpa DNS and IPv6 to evade traditional phishing defenses and are leveraging artificial intelligence to enhance every stage of their attacks, from reconnaissance to social engineering. Simultaneously, campaigns like "InstallFix" distribute infostealers through fake software installation guides. These trends underscore a critical shift towards more personalized, researched, and technically evasive attack vectors that standard security awareness may not immediately catch.
For organizations and individuals, the FBI advises heightened vigilance. Recommendations include verifying the authenticity of any payment request directly with the relevant government office using official contact information from their website—not details provided in the suspicious email. Implementing multi-factor authentication (MFA) for financial transactions and training staff to recognize sophisticated social engineering tactics are essential defensive measures. Furthermore, as the digital threat landscape grows more complex, with threats ranging from AI-powered phishing to kernel-level exploits in Windows, a layered security strategy combining user education, email filtering, and robust endpoint protection remains paramount.