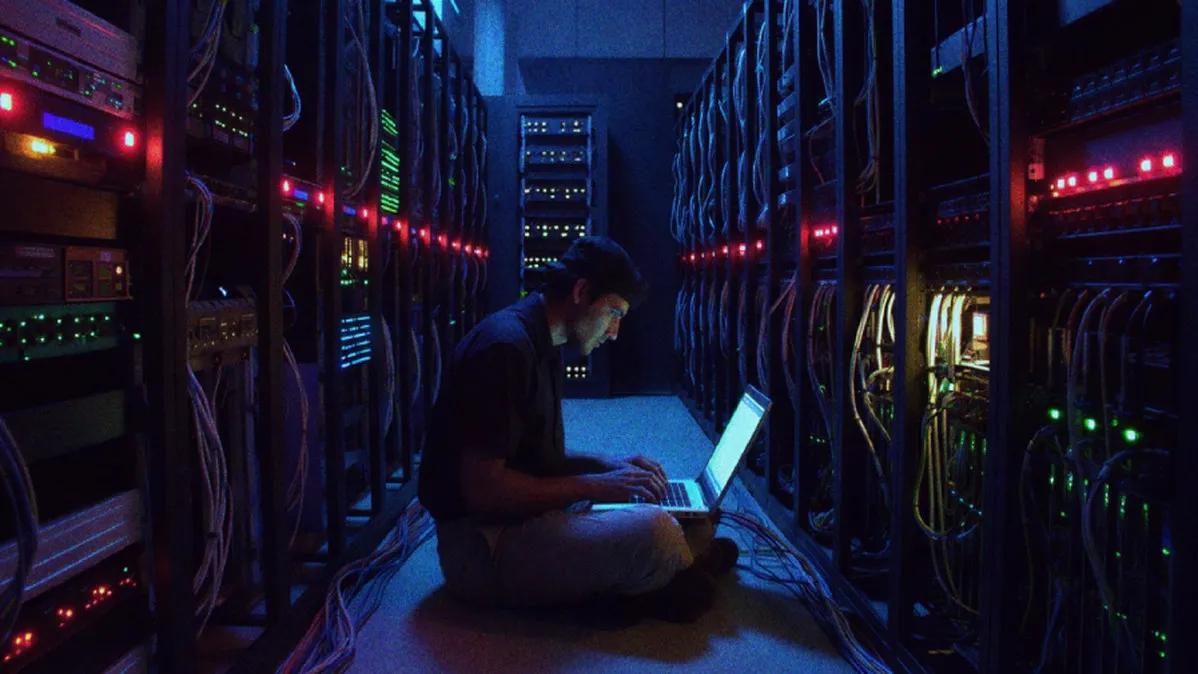
Security researchers from Broadcom's Symantec and Carbon Black Threat Hunter Team have uncovered a campaign by the Iranian state-sponsored hacking group MuddyWater, also known as Seedworm. The group has successfully embedded itself within the networks of several U.S. organizations, including a bank, an airport, a non-profit, and the Israeli subsidiary of a software company. This activity is assessed to have begun in early February, with recent intrusions detected following U.S. and Israeli military strikes on Iran. The targeted software company is a supplier to the defense and aerospace sectors, with its Israeli operation appearing to be a primary focus.
The attacks against the software company, a U.S. bank, and a Canadian non-profit were designed to deploy a previously undocumented backdoor named Dindoor. This malware leverages the Deno JavaScript runtime for execution. Broadcom also identified an attempt to exfiltrate data from the software company using the Rclone utility to transfer information to a Wasabi cloud storage bucket, though the success of this data theft is currently unknown.
Separately, within the networks of a U.S. airport and a non-profit, researchers discovered a Python-based backdoor called Fakeset. This tool was downloaded from servers belonging to the cloud storage firm Backblaze. Notably, the digital certificate used to sign Fakeset has also been used to sign other malware families like Stagecomp and Darkcomp, which have previously been linked to MuddyWater operations. This shared certificate strongly suggests the same threat actor is behind all these activities.
The findings highlight the increasing proficiency of Iranian threat actors. Their campaigns demonstrate not only evolving tooling and tactics but also a persistent focus on intelligence gathering and network footholds, particularly against entities linked to geopolitical adversaries. The use of legitimate cloud services and common runtimes like Deno and Python illustrates a trend towards blending in with normal network traffic to evade detection.