Fake IT Support Calls Unleash Havoc in New Wave of Corporate Cyber Invasions
A chilling new campaign is turning the classic tech support scam into a corporate nightmare, with hackers now using personalized phone calls to deploy advanced malware directly inside business networks. This isn't random fraud; it's a calculated precursor to massive data breach and ransomware events.
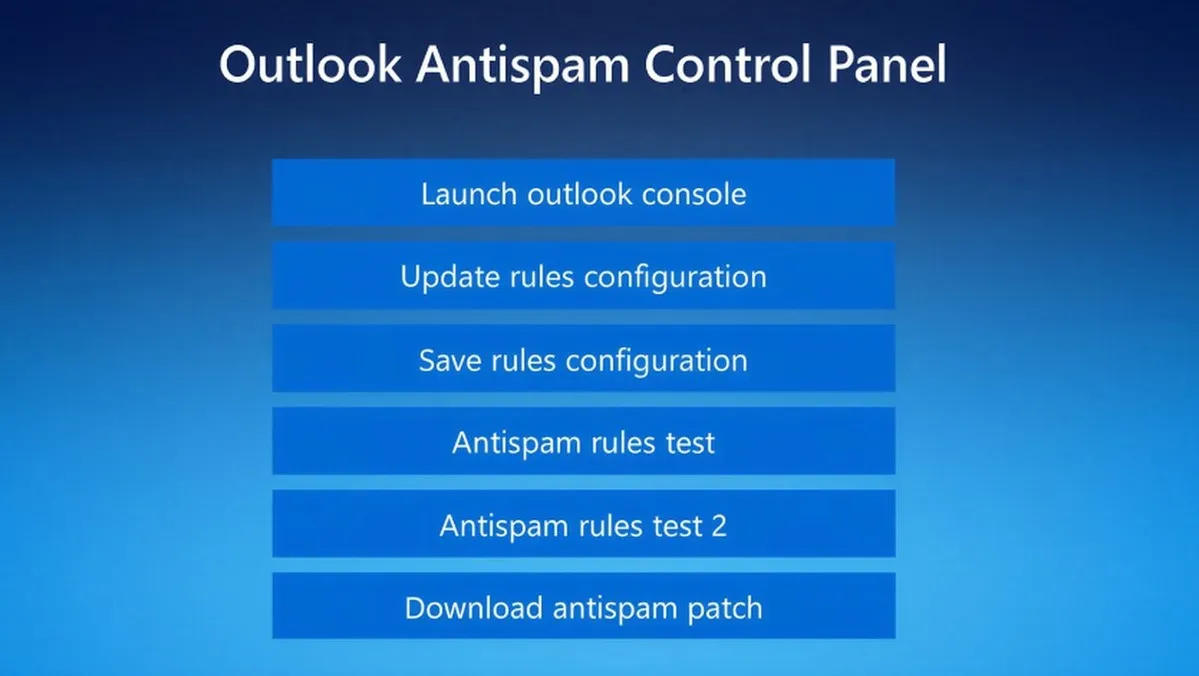
Threat hunters at Huntress have uncovered intrusions across five organizations where attackers first flooded inboxes with spam, then followed up with a phone call from a fake internal IT desk. This social engineering one-two punch tricks employees into granting remote access. Once inside, the hackers move with alarming speed, deploying a customized version of the Havoc command-and-control framework and legitimate remote management tools. In one case, they compromised nine additional endpoints in just eleven hours, a pace that screams preparation for data exfiltration or a crypto-locking ransomware attack.
The impact is severe for any organization caught unprepared. This method bypasses traditional email security filters by using the human voice as the ultimate phishing tool. The immediate risk is the theft of sensitive credentials and proprietary data, followed by the high probability of a disruptive and costly ransomware deployment. The use of legitimate tools also makes detection harder for standard defenses.
This campaign's modus operandi is a carbon copy of past attacks linked to the notorious Black Basta ransomware operation. While that group went quiet after an internal leak, its playbook is clearly still in action. This indicates either that its skilled affiliates have moved to new ransomware ventures or that rival actors have adopted this highly effective strategy. It underscores a dangerous trend: the professionalization and replication of successful social engineering exploits.
Looking forward, businesses must brace for more of these hybrid voice-and-email assaults. The seamless use of fake cloud pages to harvest passwords shows a sophisticated understanding of user behavior. My prediction is that we will see this tactic combined with zero-day exploits in commonly used remote assistance software, creating an even more potent threat.
Ultimately, this campaign is a stark reminder that the weakest link in cybersecurity is often the trusted voice on the phone, and that the road to ransomware begins with a simple, convincing lie.