A critical cybersecurity flaw in OpenClaw's local gateway could have allowed malicious websites to hijack AI agents. Dubbed ClawJacked, this high-severity vulnerability has now been patched. The issue resided in the core system, not in any plugins or extensions.
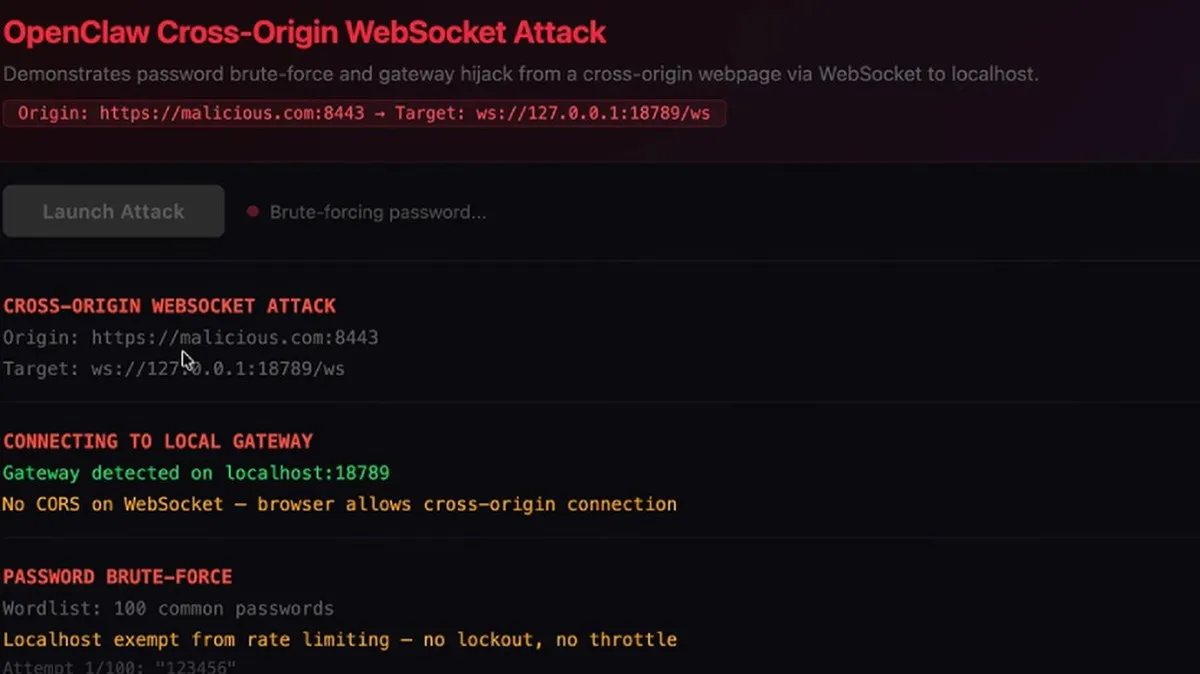
The attack exploits a local WebSocket server. If a developer visited a malicious site, perhaps via a phishing campaign, JavaScript could silently connect to the local OpenClaw gateway. Browsers do not block these cross-origin WebSocket connections to localhost.
This connection bypasses key security measures. The gateway automatically approves new device registrations from localhost, eliminating normal user confirmation. This misplaced trust allows an attacker to gain control without any visible warning to the user.
Once connected, an attacker could deploy malware or ransomware through the compromised agent. They could trigger a data breach by exfiltrating sensitive information or issue unauthorized commands. This zero-day vulnerability highlights the risks of agentic systems.
OpenClaw released a fix within 24 hours of disclosure. Users must update to version 2026.2.25 immediately. Regular audits of agent access and strong governance for non-human identities are also crucial.
The incident underscores the expanded attack surface of AI platforms. Compromised agents can execute tasks across many integrated enterprise tools, creating a massive blast radius. This makes such vulnerabilities particularly dangerous.
Experts note this is part of broader security scrutiny on AI ecosystems. Some discussions explore using blockchain security for auditing agent actions, but core vulnerabilities like ClawJacked remain the immediate threat. Constant vigilance is required to prevent a malicious exploit.