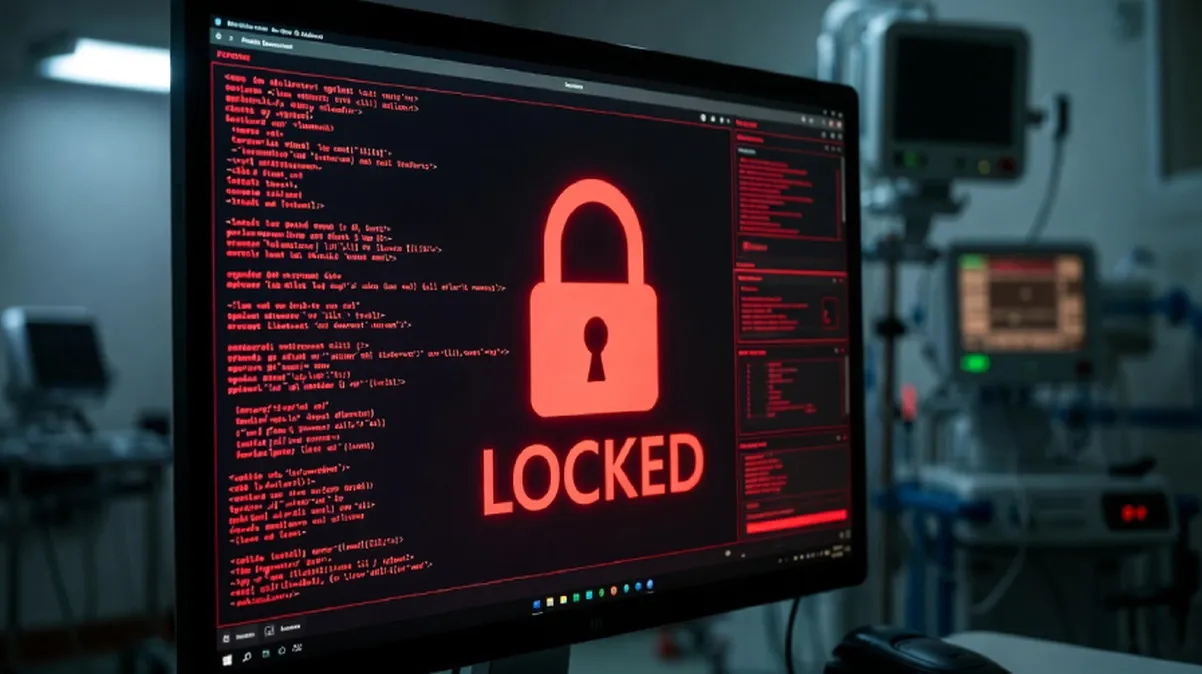
A sophisticated new ransomware campaign, attributed to the notorious North Korean state-sponsored Lazarus Group, is targeting critical infrastructure in the Middle East and healthcare providers in the United States. Security researchers have identified the operation, which deploys a variant of the Medusa ransomware, as a significant escalation in the group's tactics. The attacks leverage a previously unknown, or zero-day, vulnerability in widely used network management software, allowing the hackers to gain an initial foothold in victim systems without raising alarms.
The campaign begins with highly targeted phishing emails, meticulously crafted to appear as legitimate communications from trusted partners or internal departments. These emails contain malicious documents that, when opened, exploit the zero-day flaw to download and execute the Medusa payload. Once inside a network, the malware moves laterally, stealing sensitive data before encrypting critical files. The attackers then demand a ransom, payable in cryptocurrency, threatening to publicly release the stolen patient records and operational data if their demands are not met.
This dual-threat approach, combining data theft with file encryption, marks a dangerous evolution in ransomware strategy. For the targeted U.S. healthcare organizations, the potential data breach involves millions of patient records, including medical histories, insurance details, and social security numbers. The operational disruption caused by the encryption has forced several hospitals to delay critical procedures and revert to manual record-keeping, directly impacting patient care.
The choice of cryptocurrency for the ransom payments is a deliberate tactic to obscure the financial trail. However, analysts note that the Lazarus Group's ultimate goal may extend beyond immediate financial gain. The stolen data from Middle Eastern energy and government targets is of high intelligence value. Furthermore, the crypto ransom payments are likely funneled back to support the regime's sanctioned weapons programs, making cybersecurity a direct national security issue.
In response to the attacks, the software vendor has issued an emergency patch to address the exploited vulnerability. Cybersecurity agencies in both the U.S. and several Middle Eastern nations have released urgent advisories, urging all organizations using the affected software to apply the update immediately and to review their network logs for signs of compromise. Experts emphasize that patching is the single most critical step in preventing infection.
The broader implication of this campaign is a stark reminder of the interconnected nature of modern cyber threats. A single zero-day exploit can be weaponized against disparate sectors globally, from hospitals to oil refineries. The use of blockchain-based cryptocurrencies complicates law enforcement efforts to track and seize illicit funds. For defenders, the lesson is clear: robust email filtering, prompt patch management, and segmented networks are no longer optional. As state-sponsored groups like Lazarus continue to refine their tools and tradecraft, the line between cybercrime and cyber warfare becomes increasingly blurred, demanding constant vigilance from the public and private sectors alike.