Security researchers are tracking a new, sophisticated scanning toolkit being used by threat actors to identify networks vulnerable to the critical React2Shell flaw. Dubbed with an unfortunately provocative name, this tool allows attackers to efficiently probe internet-facing systems for the specific configuration weakness.
The React2Shell vulnerability, a severe remote code execution flaw disclosed earlier this year, remains a prime target for cybercriminal groups. This new toolkit automates the process of finding exposed servers, enabling rapid identification of high-value targets within corporate and government networks. Its deployment signals an escalation in exploitation efforts.
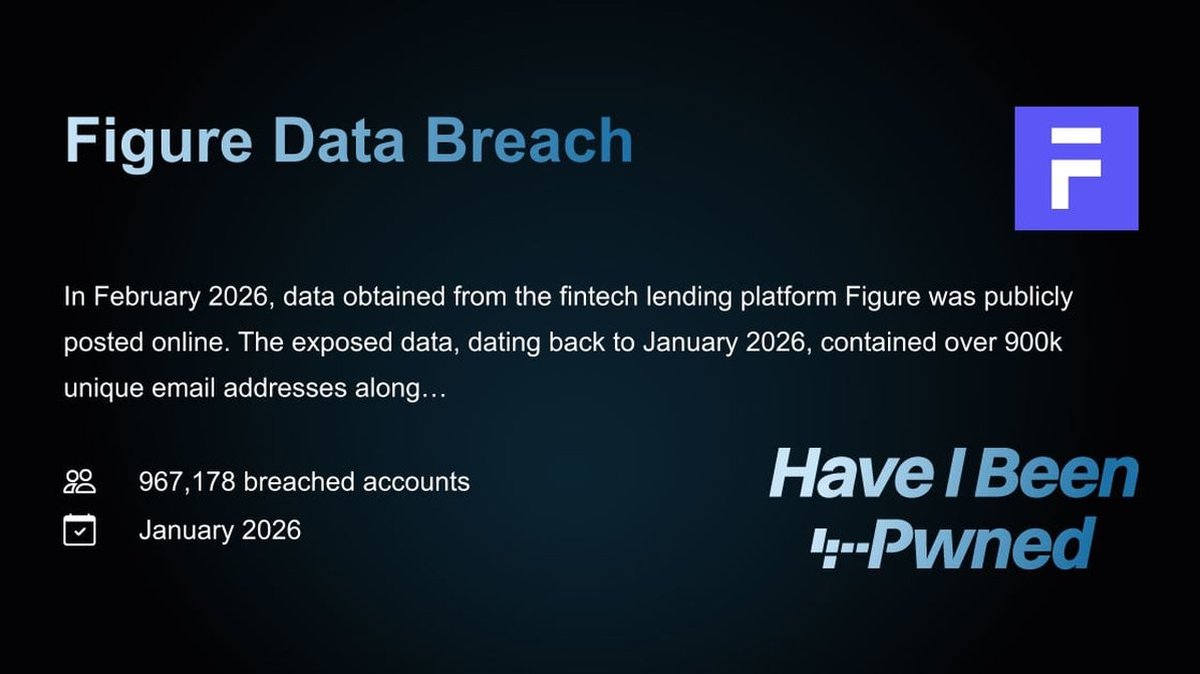
Experts warn that successful exploitation could lead to a devastating **data breach** or a **ransomware** deployment. Once inside, attackers can deploy **malware**, exfiltrate sensitive information, or lock systems for financial gain. The tool’s sophistication lowers the barrier for less-skilled threat actors to leverage this **zero-day**-level **vulnerability**.
This activity underscores the critical need for immediate patching and network segmentation. Organizations that have not applied the relevant security updates are at extreme risk. The scanning tool is particularly dangerous as it operates stealthily, often leaving no immediate trace of the reconnaissance activity.
The broader **cybersecurity** landscape continues to be shaped by the weaponization of such flaws. Alongside technical **exploit** kits, social engineering tactics like **phishing** remain a constant threat, often used in tandem to gain initial access. A layered defense strategy is non-negotiable.
In related security news, the principles of secure architecture are being applied to emerging technologies. Innovations in **blockchain security** are gaining attention, particularly for securing financial transactions and smart contracts against manipulation. However, the **crypto** asset space remains a frequent target for thieves, highlighting that all digital systems require vigilant protection.
Proactive defense is the only effective countermeasure. Continuous vulnerability management, employee training to recognize phishing attempts, and robust incident response plans are essential components of modern **cybersecurity** hygiene. Assuming your network is not a target is a catastrophic mistake.
The discovery of this scanning toolkit serves as a stark reminder. Threat actors are constantly refining their tools and tactics. In the race between patching and exploitation, delay is synonymous with defeat. Organizations must prioritize the security of their digital infrastructure now.